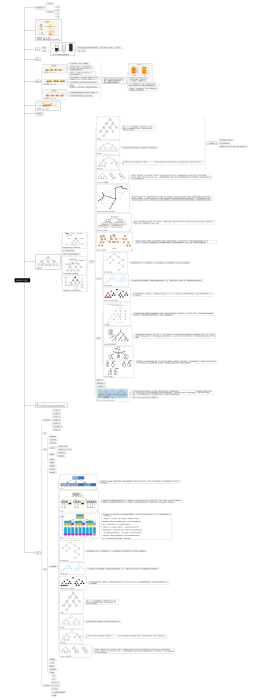
启发式测试数据结构图
2024-08-26 15:22:42 0 举报
启发式测试数据结构图
模板推荐
作者其他创作
大纲/内容
0 条评论
下一页